Cybersecurity Data Flow Diagram Cyber Security Flow Chart
Your guide to fedramp diagrams Security network diagram architecture firewall example computer diagrams cyber clipart model networks conceptdraw recommended microsoft access examples solution devices infrastructure Cyber incident flow chart
Cyber Security Flow Chart
Cyber security diagram Disadvantages of nist cybersecurity framework Security cyber framework diagram detect respond protect recover ignite systems csf categories
Flow chart of cyber investigation : cyber crime awareness society
Cybersecurity processes simple program strengthen elements data controls startSecurity network diagram control computer diagrams devices networks access model solution encryption secure examples cloud example architecture conceptdraw system software [pdf] solution-aware data flow diagrams for security threat modelingSecurity cyber network tips cybersecurity computer infographic steps diagram degrees diagrams example conceptdraw networks solutions architecture information risks threats examples.
[ #cybersecurity ] a layered defense #infographic #security #cybercrimeNetwork security model Cyber security diagramCybersecurity diagram.
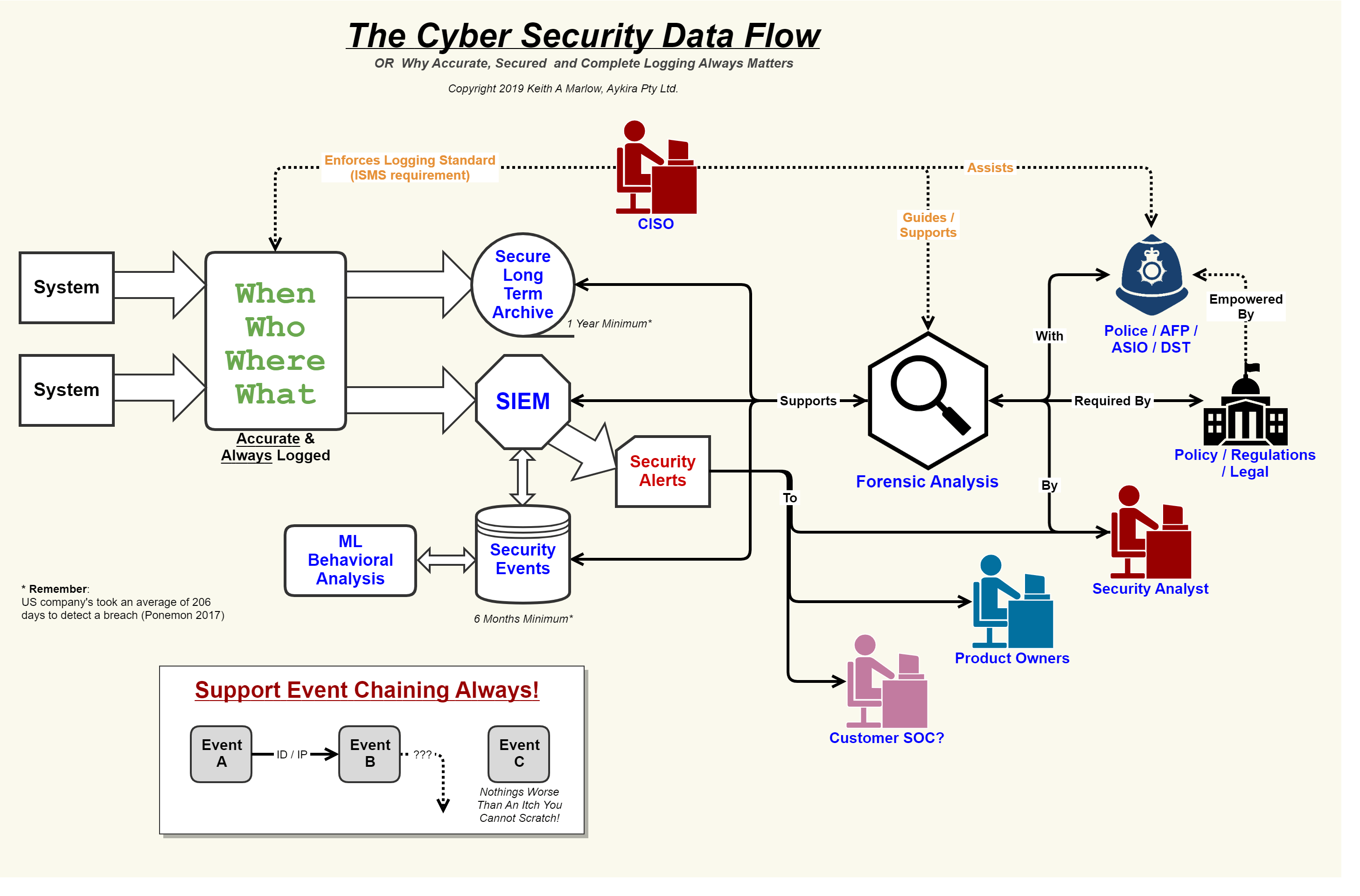
Security event logging, why it is so important – aykira internet solutions
Defense security depth cybersecurity framework profundidad defensa perimeter layers plataformas infographics sistemas frente ataque realmente segurosData flow diagram Crime evidence ipcNetwork security diagrams.
Cyber security flow chartLibreoffice draw network diagram template Cybersecurity program templateSimple processes can strengthen cybersecurity.

Cyber security framework mind map template
Machine learning in cybersecurity: a reviewCyber security flowchart Cyber security: a paradigm shift in it auditingCyber security flow chart.
Cyber security flow chartCyber security incident response flowchart Ticketing system flowchartMicrosoft graph security api data flow.

In process flow diagram data items blue prism
Network security diagramsCyber security framework Incident response life cycle diagramPin on cybersecurity.
Security flow data cyber event logging diagram internet logs important why so together showing concerning events au puttingCyber security framework mind map Cyber security flow chart.








